Governance & Risk Management , Incident & Breach Response , Next-Generation Technologies & Secure Development
Exploring the Security Requirements for Virtual Machines

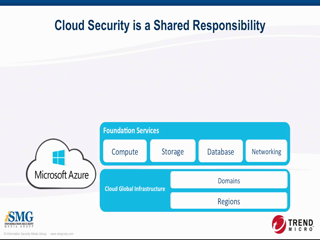
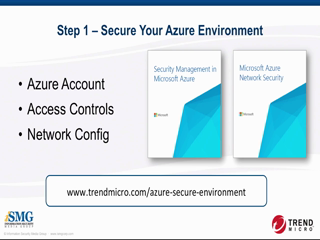
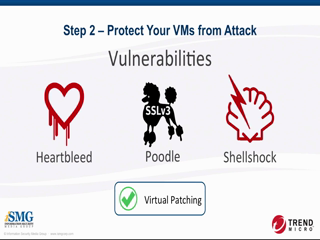
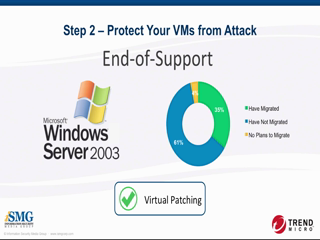
Extending workloads to cloud computing platforms offers the promise of speed and agility. But it does not relieve you of your responsibility to secure data and applications from attack. Unfortunately, traditional security approaches fall short by being incompatible with the dynamic nature of cloud and hybrid cloud environments.
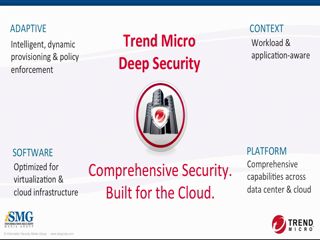
We will explore the specific security requirements for virtual machines and highlight the critical capabilities necessary to preserve the benefits of cloud and hybrid environments.