Business Continuity Management / Disaster Recovery , Cybercrime , Cybercrime as-a-service
BlackMatter Ransomware Defense: Just-In-Time Admin Access
Thoroughly Restrict Admin-Level Access to Systems, US Government Advisory Warns
How many ways do U.S. businesses need to be told to lock down their systems to safeguard themselves from ransomware?
That's the focus of a new, joint cybersecurity advisory from the U.S. government, looking specifically at attacks being launched under the aegis of BlackMatter.
"First seen in July 2021, BlackMatter is ransomware-as-a-service tool that allows the ransomware's developers to profit from cybercriminal affiliates - i.e., BlackMatter actors - who deploy it against victims," the advisory says. "BlackMatter is a possible rebrand of DarkSide, a RaaS which was active from September 2020 through May. BlackMatter actors have attacked numerous U.S.-based organizations and have demanded ransom payments ranging from $80,000 to $15 million in bitcoin and monero."
The advisory urges organizations to use newly published intrusion detection signatures to help spot and block BlackMatter attacks, as well as to use strong passwords, implement multi-factor authentication wherever possible, keep all systems patched and updated, limit network access, segment networks and watch for unauthorized network traversal, and maintain good data backup and restoration practices.
Getting the Message?
If such advice seems obvious, or indeed the form of this advisory looks familiar, perhaps it's because it follows the joint advisory issued last month by CISA, FBI and NSA for Conti ransomware.
How many different ransomware advisories do businesses need to receive before they take decisive action?
For years, the top-line advice being issued from cybersecurity officials has included the above advice. Not least, they have urged all organizations - whether or not they think they might be a target - to ensure they always maintain and test complete backups, stored offline, so they can wipe and restore any systems that get hit by ransomware.
BlackMatter TTPs
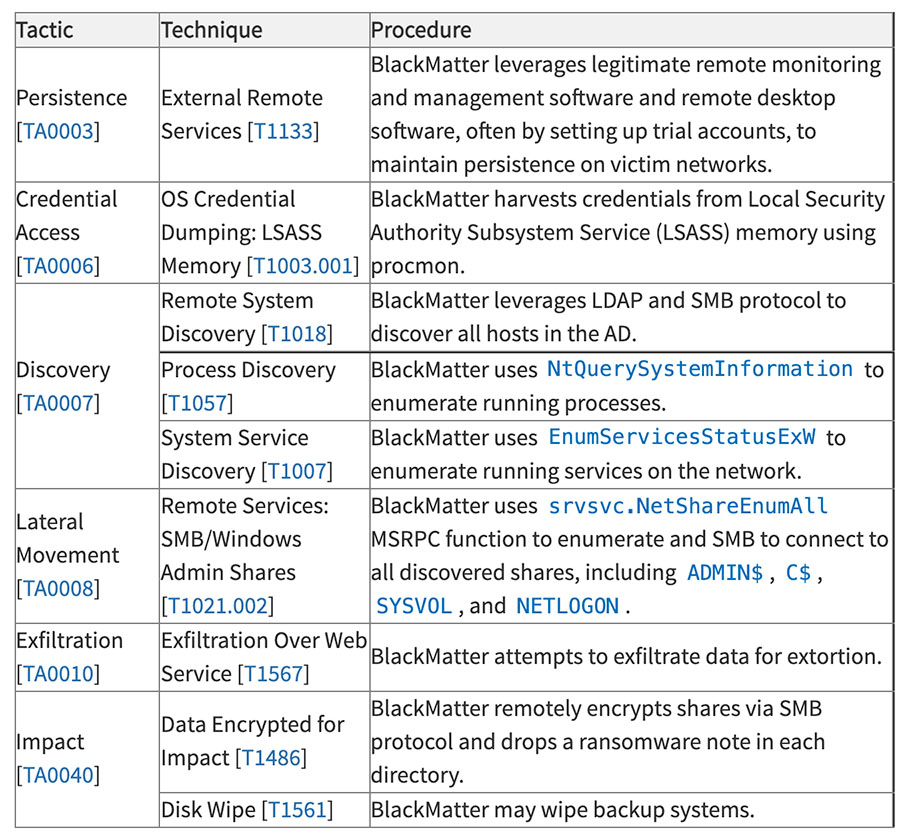
To be fair, the BlackMatter alert, beyond including intrusion system rules, also details the group's known tactics, techniques and procedures, and includes additional recommended defenses, such as implementing "time-based access for accounts set at the admin-level and higher," due to ransomware-wielding attackers' propensity to attack organizations after hours, over weekends, on Christmas Eve or any other inconvenient time.
What does time-based access look like? One approach is just-in-time access, which enforces least-privileged access except for temporarily granting higher access levels via Active Directory.
"This is a process where a network-wide policy is set in place to automatically disable admin accounts at the AD level when the account is not in direct need," according to the advisory. "When the account is needed, individual users submit their requests through an automated process that enables access to a system, but only for a set timeframe to support task completion."
Initial Access Possibilities Abound
The long list of fresh ransomware victims bespeaks many organizations not yet having gotten the message about the above types of needed defenses (see: Ransomware Patch or Perish: Attackers Exploit ColdFusion).
Indeed, in August, a representative of the LockBit 2.0 ransomware group called "LockBitSupp" told an interviewer that "the victims who are paying are the ones who do not make backups and poorly protect sensitive information, regardless of the industry."
Another measure of how not-locked-down many victims continue to be comes in the wake of security firm Trustwave last week releasing a free decryptor for a newer type of ransomware called BlackByte, after it recovered a sample while helping an organization respond to the attack.
Of course, that's good news. But when I asked Karl Sigler, the senior security research manager for Trustwave SpiderLabs, how the ransomware had first infected the victim they assisted - for example, if it was due to attackers brute-forcing their way into the organization's remote desktop protocol connection, or perhaps using known, common vulnerabilities and exposures, to exploit an unpatched VPN server - he said there had been so many potential ways in that it probably didn't matter; attackers had multiple options.
"We do not know what the initial attack vector was, but it's likely not that important," he told me. "The malware could have been dumped via CVE exploit, misconfiguration, lack of patching, social engineering like phishing, etc. Unless there's a pattern that needs to be tracked as common tactics, techniques and procedures, or TTPs, which is not the case here to our knowledge. The initial attack vector is not important."
Everyone is a Potential Victim
The joint advisory is also a reminder that any organization can become a victim.
Despite numerous ransomware operations claiming they never knowingly hit so-called critical sector organizations - an expansive definition that includes everything from agriculture and healthcare to food and banking - such targets get regularly hit.
DarkSide's exit and rebrand as BlackMatter appears to have been driven by the former incarnation hitting Colonial Pipeline Co. on May 7, disrupting fuel deliveries to much of the U.S. East Coast. After Colonial Pipeline paid attackers $4 million in bitcoins - much of which the FBI managed to recover - DarkSide blamed the attack on an affiliate and claimed that it was shutting down.
Some pundits have asked if ransomware groups, which are predominantly Russian-speaking, might be serving as a proxy cyber force for Moscow. But many cybersecurity experts say ransomware-wielding criminals just seem to have an opportunistic "attack first, ask questions later," attitude when it comes to target selection. If they find a weakly secured network, it seems to be fair game, and if it happens to belong to a hospital or national health service, then maybe they'll offer a free decryptor later. But even with a decryptor, recovering from a ransomware attack is often not a trivial matter.
The better move remains, whenever possible, to not get infected in the first place. And as a backup, literally maintain backups. After consultancy Accenture disclosed in August that it had gotten hit, via an attack it detected, for which LockBit 2.0 took credit, the attackers threatened to dump data they'd stolen unless they received a ransom payment. As LockBit shortly thereafter dumped the stolen data, Accenture apparently didn't pay, but rather just restored from backups. Defensively speaking, that remains one of the best ways to make a potentially long ransomware story short.











