Cybercrime , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime
Feds Warn of 'Electricfish' Malware Linked to North Korea
CERT Says Hidden Cobra APT Group Developed Malware
The FBI and the Department of Homeland Security have issued a joint warning about new malware called "Electricfish." Investigators suspect it was developed by the advanced persistent threat group Hidden Cobra, which has been linked to North Korea.
See Also: Bank on Seeing More Targeted Attacks on Financial Services
A warning released by the U.S. Computer Emergency Readiness Team on Thursday does not indicate if any organizations have sustained an attack from Hidden Cobra, also known as the Lazarus Group, using the Electricfish malware. Because investigators were able to reverse-engineer some of the code, however, there's a possibility it is operating in the wild and has been used in some way by the group.
New Warnings
This is the second time within a month that U.S. authorities have warned about new cyberattacks stemming from Hidden Cobra, which has been linked to the WannaCry ransomware attacks of 2017 as well as the Sony Pictures breach of 2014.
In April, CERT warned of Hidden Cobra using a new Trojan called Hoplight that can disguise the network traffic it sends back to its originators, making it more difficult for security companies and law enforcement officials to track its movements (see: US CERT Warns of N. Korean 'Hoplight' Trojan).
Over the last two years, CERT has issued 17 warnings about cyberattacks tied to North Korea, starting with the initial WannaCry alert.
Tunneling Malware
The primary purpose of Electricfish is to secretly funnel traffic between two IP addresses using a custom protocol, allowing the attackers to steal data and avoid detection.
This type of "hidden tunnel" between two IP address is sometimes used in legitimate business applications, but attacks can use this method for data exfiltration, says Chris Morales, head of security analytics at Vectra, a San Jose, California-based threat detection and response firm.
"This type of connection, using a custom protocol instead of existing protocols like HTTP, are what we refer to as hidden tunnels and are used for command and control of remote systems as well as for data exfiltration," Morales says. "Hidden tunnels used as part of a targeted attack are meant to slip by an organization's perimeter security controls and indicate a sophisticated attacker."
The analysis of the Electricfish malware is based on one 32-bit Windows executable file that contains the custom protocol that allows network traffic to be funneled between a source IP address and a destination address, according to CERT.
Through reverse-engineering, federal investigators found that the malware continuously attempts to reach out to both the source and destination systems. By doing this, it allows the attackers on either side to start a funneling session. Electricfish can also be configured with a proxy server or port as well as a proxy username and password, the analysis found.
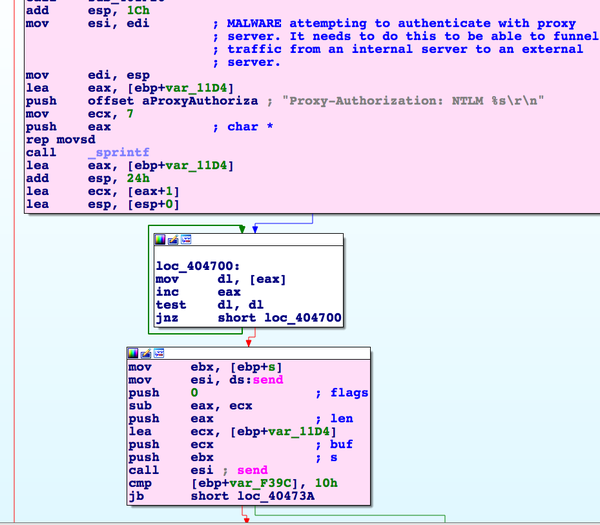
"The application accepts command-line arguments allowing it to be configured with a destination IP address and port, a source IP address and port, a proxy IP address and port, and a user name and password, which can be utilized to authenticate with a proxy server," according to the CERT analysis.
The malware will also attempt to establish a transmission control protocol between the source and destination IP address. If that connection is made, it then creates the custom protocol that allows traffic to flow rapidly between two machines, the analysis notes.
"After the malware authenticates with the configured proxy, it will immediately attempt to establish a session with the destination IP address, located outside of the target network and the source IP address," according to the alert.
These features in the Electricfish malware allow the "actor to bypass the compromised system's required authentication to reach outside of the network," according to the analysis. This is designed to funnel data out of the target's network without alerting the victim. It also helps keep the attack and the true motives hidden from the security staff, CERT finds.
Warning to Businesses
As with other warnings from CERT, the FBI and DHS are urging organizations to take some precautions to prevent an attack. These include:
- Maintain up-to-date anti-virus signatures and engines and keep operating system patches current;
- Disable file and printer sharing services when possible; use strong passwords or Active Directory for authentication;
- Restrict users from installing and running unauthorized software;
- Disable unnecessary services and software as well as workstations and servers;
- Scan and remove suspicious email attachments, and ensure that attachments are "true file types" - the extension matches the file header.