DDoS Protection , Governance & Risk Management , Security Operations
IBM Blamed for Australian Census Debacle
Australian Bureau of Statistics Claims IBM Didn't Manage Risks
The Australian Bureau of Statistics has laid the blame on IBM for failing to stop distributed denial-of-service attacks that crippled its website last month on the evening of the country's largest-ever online census.
See Also: Overcoming Today’s Escalating Cyberthreats
The ABS says that DDoS attacks should not have been able to disrupt the census, which was hosted on IBM's infrastructure.
"Despite extensive planning and preparation by the ABS for the 2016 census this risk was not adequately addressed by IBM, and the ABS will be more comprehensive in its management of risk in the future," according to an ABS report that has been submitted to the Senate Economics References Committee.
But Steve Wilson, a vice president and principal analyst with Constellation Research in Sydney, says it appears to be premature for the ABS to lay the blame on IBM so pointedly and categorically for the two-day census site meltdown.
"To go public with these claims which IBM cannot answer is brash, because as we all know, you cannot outsource accountability," Wilson says. "On its face, unless and until negligence can be proven, ABS has to wear a great deal of the formal responsibility."
IBM officials did not have a comment on the report. IBM has been a longtime partner of the ABS, which in 2014 awarded the tech giant a $9.6 million contract for the design and development of this year's online "eCensus" project.
Census Goes Down
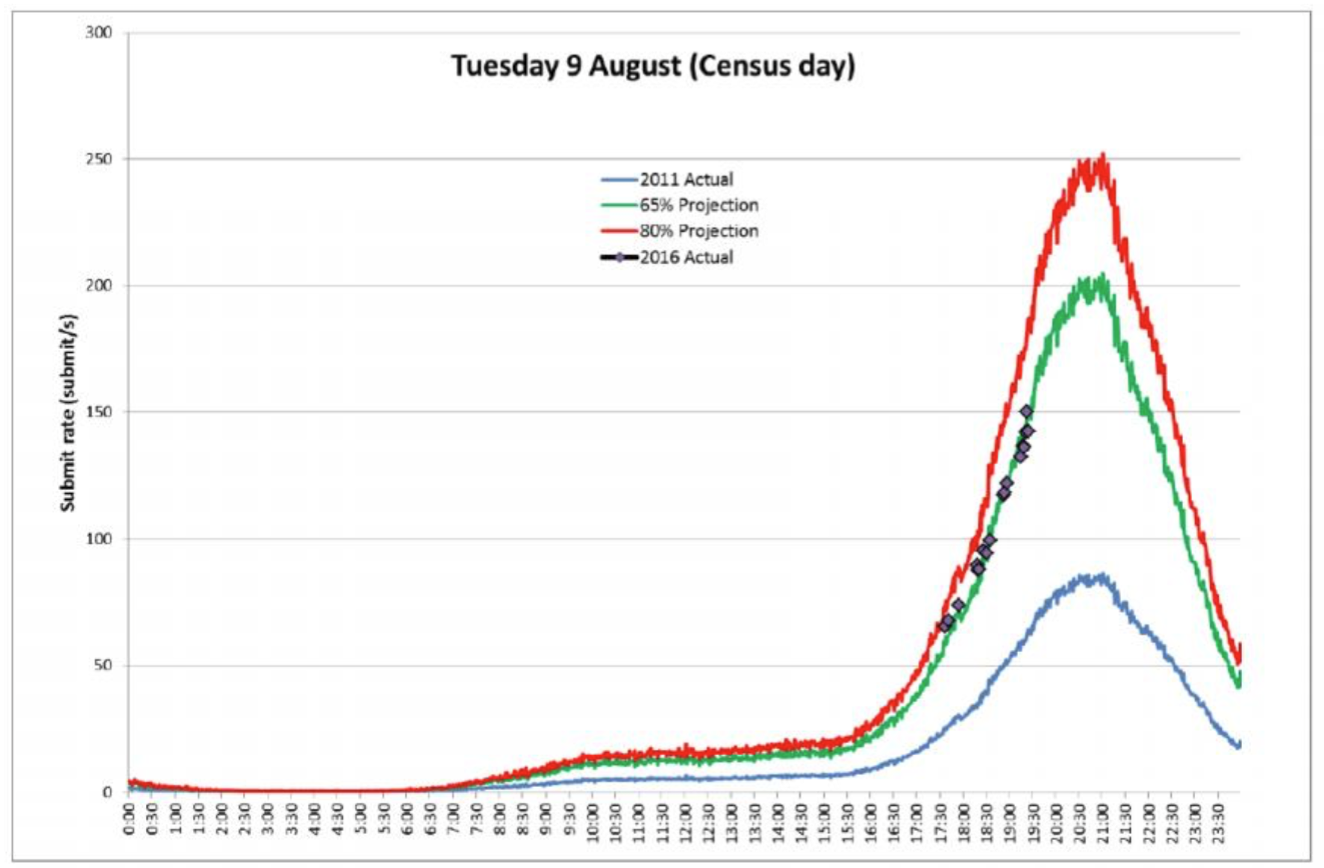
The online census form went offline at 7:33 p.m. on Aug. 9, the day the ABS had encouraged Australia's 23 million-strong population to complete the form or face fines. The site was hit with three small DDoS attacks, which flood websites or other systems with junk traffic.
Following a fourth DDoS attack and growing fears that census data might have been compromised, the ABS elected to keep the systems offline. About two days later, service was restored.
The ABS, working with the Australian Signals Directorate - Australia's sister intelligence agency to the U.S. National Security Agency - quickly determined that no data had been stolen. But the incident shook confidence in the government's ability to execute large-scale technology projects. It also followed a privacy uproar triggered by extensions to the time period in which the ABS retains census data (see Australia in Privacy Furor Over Census).
Fault: DDoS or Census Takers?
A technical section contained in the new ABS report largely confirms information about the census site meltdown that has been previously disseminated. But it also omits details that would provide more clarity around exactly what happened.
All of the DDoS attacks originated from overseas, the report says. The first two attacks occurred in the morning, and both briefly disrupted the census form for a few minutes. A third attack, at 4:52 p.m., caused no disruptions. But the fourth one at 7:32 p.m. was different - it was a DNS reflection attack, according to the report.
The Domain Name System is the internet's addressing system that translates domain names into IP addresses. A request is made to a DNS resolver, which delivers an answer that allows the browser to go to the correct IP address.
In a DDoS reflection attack, large volumes of DNS queries are directed at a victim's DNS resolvers - in this case the ABS's - to overload their systems.
Concurrent with the fourth attack, ABS and IBM noticed "an unusual spike in outbound traffic," which could have been a sign that census data might be being stolen, which is when the ASD was brought in. The ASD later figured out what caused the spike, but the report inexplicably omits the reason.
Soon after the fourth attack, IBM's border routers failed, and an initial attempt to reboot the equipment was unsuccessful, the report says.
When planning the online census, the ABS and IBM had anticipated that DDoS attacks could occur, the report says. IBM had a plan that involved blocking overseas traffic to the census website, a step referred to in the report as "Island Australia" or geoblocking.
But the ABS says it relied on IBM's assurances that its DDoS defenses would be adequate.
"At no time was the ABS offered or advised of additional DDoS protections that could be put into place," the report says. "Additionally, no suggestion was made to the ABS that the DDoS protections that were planned were inadequate."
Wrong Conclusion Reached?
Technical experts with companies that have broad visibility into international internet traffic said they didn't notice unusual attacks aimed at Australia on Aug. 9. But it also doesn't take much traffic to knock an ill-prepared service offline, and DDoS traffic is a constant presence on the internet.
Some security experts have also theorized that the ABS might have mistaken droves of legitimate Australians - who were trying to access the census - for a DDoS attack. Many Australians use DNS resolvers that are located outside the country.
Hence when IBM activated geoblocking, those people would have been unable to access the census. What IBM and the ABS would have seen on their network could have thus been misinterpreted as a DDoS attack: lots of repeated, inbound DNS queries. But the traffic should have been expected, since the ABS encouraged everyone in the country to complete the census on the evening of Aug. 9.
The report doesn't address this scenario or theorize about the identity of the alleged attackers. No hacking group has ever claimed credit for disrupting the census.
Before the census site went offline, 2.2 million people had completed the form. After it came back online, the ABS says 2.6 million households completed it. Despite the outage, the ABS says that 59 percent of completed census forms were ultimately submitted online.