Endpoint Security , Fraud Management & Cybercrime , Incident & Breach Response
Ransomware: Why Some Victims With Backups Still Pay
Also, DHS Pitches Post-WannaCry 'Active Defense' to the Private Sector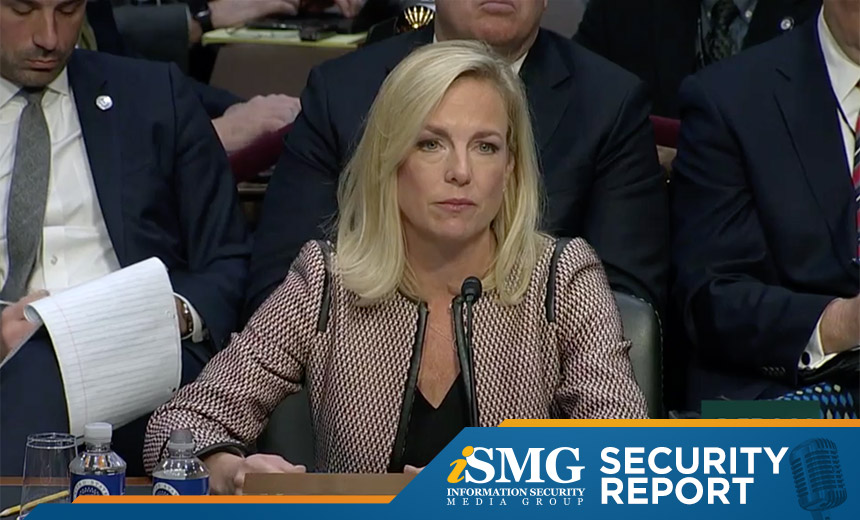
Leading the latest edition of the ISMG Security Report: Why some organizations with working backups still choose to pay a ransom after suffering a cryptolocking malware attack.
In this report, you'll hear (click on player beneath image to listen):
- HealthcareInfoSecurity Executive Editor Marianne Kolbasuk McGee describe why some ransomware victims meet attackers' ransom demands to get up and running more quickly, even though they have working backups;
- ISMG Managing Editor for Security and Technology Jeremy Kirk analyze BlackBerry's move to secure autonomous cars.
- Homeland Security Secretary Kirstjen Nielsen testifying before the Senate Judiciary Committee on Tuesday about DHS's efforts to work with the private sector and bolster their "active defenses."
The ISMG Security Report appears on this and other ISMG websites on Tuesdays and Fridays. Don't miss our Jan. 12 and Jan. 16 reports that respectively analyze FBI Director Christopher Wray's controversial comments about encryption and the move by U.S. healthcare companies to comply with the EU's General Data Protection Regulation.
The next ISMG Security Report will be posted on Tuesday, Jan. 23.
Theme music for the ISMG Security Report is by Ithaca Audio under a Creative Commons license.


















