LulzSec: Senate, Sony Hackers Profiled
'Pick a Target and We'll Obliterate It'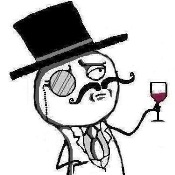
"Pick a target and we'll obliterate it. Nobody wants to mess with The Lulz Cannon." - LulzSec on Twitter
With that tweet around midday Tuesday, the group that claims it breached the Senate, CIA, Sony and other organizations gave a phone number with a Columbus, Ohio, 614 area code to call. By day's end, Lulz Security tweeted it missed 5,000 calls and received 2,500 voicemail messages. "You have reached the whistle box of Pierre Dubois François Lulz," the altered, faux-French-accented voice on the message machine said. "We are not present right now because we are busy ruining your Internet. Leave a message, and we will get back to you whenever we can."
Those behind LulzSec seem to be boys (perhaps girls, too) just wanting to have fun. Lulz is a verbalization of LOL, laughing out loud. LulzSec's symbol of a monocled, mustached dilettante holding a wine glass suggests the group doesn't take itself seriously. They're a playful bunch making online mischief. "The world's leaders in high-quality entertainment at your expense," LulzSec touts on its Twitter page. Go to its homepage and you'll hear Jack Jones singing the Love Boat theme from the popular TV show of the '70s and '80s. As Jones croons, you can sing along with lyrics posted on the page tailored for "The Lulz Boat." Hit the word "mute" on the homepage screen, and the music gets louder.
But their mischief goes beyond schoolboy pranks. Click on the link "Releases" and you'll go to a page that lists their attacks that started the afternoon of April 22 when it hacked into the database of the Fox-TV's X-Factor 2011 contestants' contact information, exposing the names, birthdates, e-mail address and phone numbers of more than 73,000 entrants in the talent contest. "Some of them feel like Robin Hood, benevolent anarchy," Josh Corman, research director at The 451 Group, an IT analysis and research firm, says of LulzSec members. "But others see them as chaotic evil, like the Joker."
Who else has LulzSec hacked? According to LulzSec, victims include game-maker Bethesda Software, Fox.com, Infragard Atlanta, PBS, Senate.gov, Sony, UK ATM and Unveillance.
He Said, She Said
The owner of the botnet monitoring service Unveillance is an example of LulzSec wanting to teach an individual a lesson. When LulzSec hacked FBI-affiliate Infragard Atlanta, it obtained the identity and passwords of about 180 users, some of whom used the same passwords on other systems, a practice highly discouraged by the FBI. One of the pilfered passwords belonged to Univeillance CEO Karim Hijazi. LulzSec said Hijazi used the same password for his Gmail account and Univeillance login. Using the password, LulzSec said it stole his personal and corporate e-mails and it briefly took over Univeillance servers and botnet control panel. Hijazi contends he used different variations of the same password, and LulzSec figured out the actual ones for other systems. He conceded he should have used two-factor authentication. Hijazi also disputes LulzSec contention that it gained control of the company's servers or botnet control panel. "Had we agreed to provide this data to them, LulzSec would have been able to grow the size and scope of their DDoS attack and fraud capabilities," Hijazi said in a statement.The story gets juicier. LulzSec contacted Hijazi and fessed up. Hijazi, according to LulzSec, offered to pay the hackers to keep quiet, and offered more money to destroy his competitors. Hijazi's version is quite different, contending LulzSec tried to extort him to reveal sensitive data about Univeillance's botnet intelligence that would have put his customers at risk from massive distributed denial of service attacks. In a posting on pastebin.com, LulzSec responded: "We were never going to extort anything from you. We were simply going to pressure you into a position where you could be willing to give us money for our silence, and then expose you publicly." Hijazi said he has contacted the United States Computer Emergency Readiness Team and FBI, who are investigating the breach.
It's not easy to read into LulzSec's motivation. Like early hackers, they seek to punish those with different ideologies. They also seem intolerant of those who know the rules but fail to follow them, such as IT security professionals who reuse passwords. "But it's more brazen this time around," 451's Corman says. "They're in it for the laughs."
'Game Is On, Folks'
Indeed, LulzSec combines arrogance and humor, as in this tweet about /b/tards, users of online imageboards who can be very callous toward each other: "The best part about making 50% of all /b/tards our bots is that they leave their daddy's laptops on 24/7, more bandwidth for us." Still, mischief seems part of their being. Take this past Tuesday, when the Internet was flooded with reports that LulzSec hacked the Senate (see Group Claims Hack on Senate Computers), the group took aim at the online gaming community, including the magazine The Escapist, EVE Online, Minecraft and League of Legends as well as an IT security company called Finsisher, according to LulzSec tweets. "We're firing at Escapist Magazine with around 0.4% of our total ammunition," a LulzSec tweet said. "Let's see what their admins are made of - game is on, folks."
Early Wednesday afternoon, LulzSec posted a tweet saying it can redirect its phone numbers anywhere, and solicited suggestions. Less than 10 minutes later, at 1:35 p.m., it posted: "FBI in Detroit just got hundreds of calls. That woman was mad." Contacted a few minutes later, two employees at the FBI field office in Detroit said they were unaware of a call blast directed at them.
LulzSec is a pest for a growing number of organizations, and their activities have highlighted the unpreparedness of many organizations to safeguard properly their IT assets. And, they've caused some damage and inconvenience, but even more so, embarrassment. LulzSec claimed late Wednesday it hacked the CIA website - "Tango down - cia.gov - for the lulz" - yet there seems to have been no significant damage to the site. They're not the Chinese or Russians, trying to pilfer national, military or trade secrets, but individuals who, perhaps, could be employees of the organizations they target. "These are ideological insiders that have access; this is more like Fight Club; they do your laundry, they work in the mailroom," Corman said. "This is a whole counterculture thing; especially in a time when people feel powerless. They find this empowering."