Governance & Risk Management , Incident & Breach Response , Security Operations
Microsoft Advocates 'Digital Geneva Convention'
The Agreement Would Aim to Protect Civilians, Critical Infrastructure
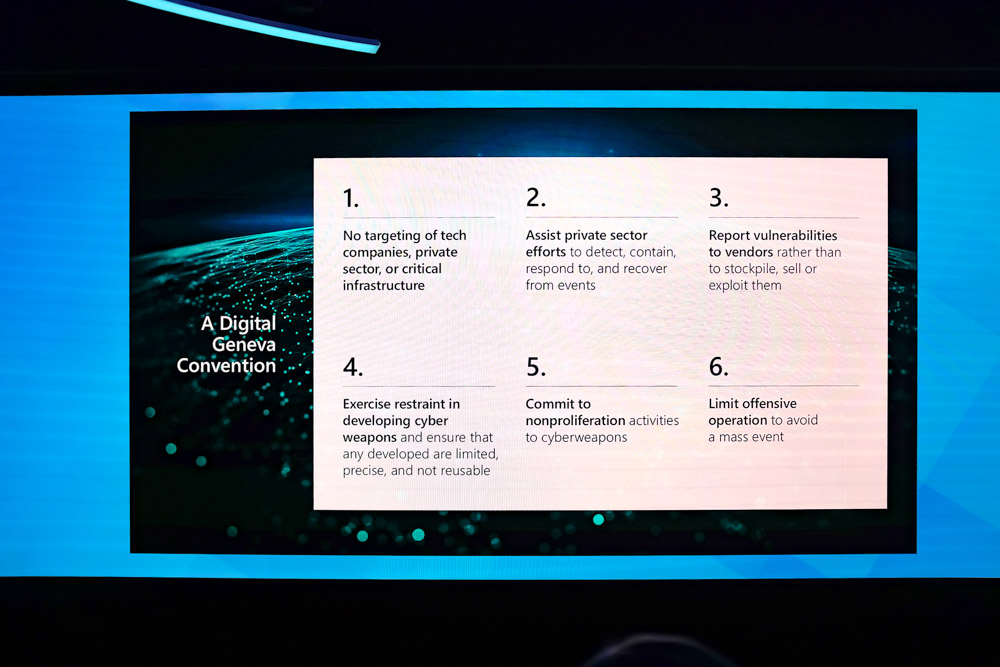
Are there rules in cyberspace? There aren't many, but Microsoft is proposing a "Digital Geneva Convention" that would set internet norms for countries to help prevent unfair targeting of civilians.
See Also: Break the Fraud Lifecycle
Microsoft President and Chief Legal Officer Brad Smith says governments should craft an international agreement that protects civilians from nation-state cyberattacks, with defensive assistance from technology companies that run the majority of internet infrastructure.
Smith, who published his proposal, keynoted the RSA Conference 2017 in San Francisco Feb. 14. He said that nation-state hacking has evolved to attacking civilians during peacetime, a move that demands new rules of engagement.
"We suddenly find ourselves living in a world where nothing seems off limits to nation-state attacks," Smith said. "There are increasing risks of governments attempting to exploit or even weaponize software to achieve national security objectives."
His proposal would commit governments to implementing norms designed to protect civilians on the internet in times of peace, in the same spirit as the Fourth Geneva Convention of 1949. Governments should agree to not conduct cyberattacks against the private sector, specifically stealing intellectual property, or critical infrastructure, he said.
Such a "digital convention" should also set up an independent organization that brings the public and private sectors together to investigate and release detail publicly on nation-state attacks, he added.
Cyber Under International Law
Efforts have been underway for a number of years to develop international law to address cyber activity, says Kenneth Geers, senior research scientist with Comodo and a former research scientist with the NATO's Cooperative Cyber Defence Centre of Excellence.
As the hacking of political parties in the U.S. during the recent presidential campaign shows, the law needs to catch up because cyberattacks are changing the landscape of national security, he tells Information Security Media Group.
"There's very little stopping this kind of activity," Geers says. "If you think about it from a legal perspective, it's very important. We should be looking at a lot of legal aspects because it's really the law - at least in Western society - that's supposed to tell you what you can and can't do."
As commerce and communication moved to internet-based platforms, it was expected war would as well. The huge benefit of launching a network-based attack is it avoids the messy consequences of kinetic warfare.
Cyberattacks can be extremely effective and disruptive. While it's virtually impossible to drop a bomb without knowing which nation is behind it, cyberattacks are shrouded in confusing technical tricks, leading to much speculation but often lacking dead-set proof of who was responsible.
The most striking recent example is the U.S. government's belief that Russia mounted an extensive hacking and disinformation campaign prior to the 2016 presidential election. The output from the effort, from leaked embarrassing emails to fake news stories, clouded an already unconventional political campaign. It also has alarmed other nations, which fear election disruption may be seen as fair game by their enemies (see Australia to Warn Political Parties of Hacking Risks).
Private technology companies are often the first to notice suspected state-sponsored activity. In 2010, Google took the unprecedented step of accusing China of targeting dissidents in Operation Aurora, which sought access to Gmail accounts.
Slow Progress
There has been progress, albeit slow, in at least discussing boundaries. In September 2015, the U.S. and China signed an agreement in which both governments pledged to not support the theft of intellectual property through cyberattacks (see U.S.-China Cybersecurity Agreement: What's Next?).
The agreement came 16 months after mounting U.S frustration with suspected Chinese-led attacks on private U.S. organizations. In May 2014, the U.S. took the unprecedented step of charging five Chinese Army signals intelligence officers with stealing trade secrets from companies and organizations in the nuclear, solar power and steel industries. China denied the accusation (see The Real Aim of U.S. Indictment of Chinese).
Following the agreement, security companies said they noticed diminished activity originating from China, which at least circumstantially validated using diplomacy to approach cybersecurity issues.
Also, a United Nations group composed of 20 countries in July 2015 proposed "limiting norms" that nations should abide by on the Internet. The recommendations include the ban of activity that damages national critical infrastructure or using their computer emergency response teams for malicious activity.
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.