New 'Sweetheart' Schemes Exploit Mobile
Fraudsters Abuse RDC Services for Fraudulent Checks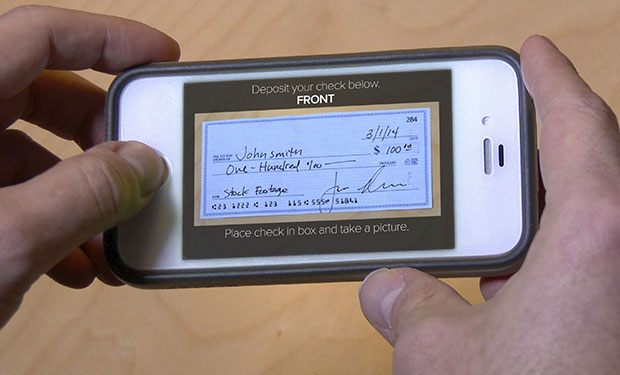
A resurgence in so-called "sweetheart" bank fraud schemes has gotten the attention of banking institutions throughout the country.
See Also: Email's Need For The Security Advantages of Cloud Infrastructure
While these types of socially engineered schemes, which prey on users of online dating sites, have been around a long time, recent schemes have been linked to the exploit of mobile banking and remote-deposit-capture used for fraudulent and counterfeit checks.
This week, Guardian Analytics, a behavioral analytics firm, released a report about recent upticks in sweetheart scams. Like most socially engineered schemes, banking institutions have a difficult time stopping and detecting sweetheart schemes because they involve the willing participation of a legitimate accountholder, says Craig Priess, Guardian Analytics' president.
"This is not an authentication problem, he says. "In this case, you have different credentials used by a legitimate accountholder that are given to the criminal," he says.
These new-age sweetheart schemes highlight the need for comprehensive cross-channel fraud detection, as well as better customer education, experts say. Until customers understand the risks associated with some of these emerging socially engineered attacks, fraudsters will continually find new ways to exploit consumers and the numerous banking channels they use, Priess says.
"This is a social engineering scheme tied with technology, and the money comes in and out a number of different ways," he says. "There is really no one thing to look for, which makes this a difficult scheme for banks to detect."
Mobile Sweetheart Scheme
The scheme Guardian Analytics uncovered involves fraudsters persuading their victims to either provide them access to an existing bank account, with login credentials, or open new accounts the fraudsters can access. From there, the criminal sets up mobile access to the account, typically enabling remote-deposit-capture deposits.
With RDC, fraudsters can deposit fraudulent and counterfeit checks into the accounts through the banking institution's mobile app and then access the funds without the victims' knowledge.
"There are three variations for getting the money out," according to the Guardian Analytics report.
One way involves asking the victim to send the fraudster a debit card to access funds deposited into the account, enabling the scammer to cash out at an ATM, the report states. "This version may be harder to detect because the victim likely is unaware of how the criminal is using the compromised account," according to the report.
Other variations involve asking the victim to transfer funds, by wire or money-remittance, to the criminal, or by transferring the funds to an online account controlled by the fraudster.
"Social engineering is definitely on the upswing, simply because of all of the different ways customers are being targeted," Priess says. "You are dealing with savvy criminals, and there are a ton of variations, which makes these schemes very difficult to detect through specific patterns. You can't find all of the patterns and variations, so you really have to focus on accountholder behavior."
Education plays a leading role when it comes to thwarting these attacks because the victims are unknowingly helping the fraudsters perpetrate the crime, he adds.
"We have seen examples of the bank calling their customer to verify a certain wire transfer or cash withdrawal and the accountholder confirms the activity, so the bank lets it happen," Priess says. "Then, a week later, the accountholder realizes they've been duped and it's too late."
Banking institutions often catch these scams before the victims, says fraud expert Avivah Litan, an analyst at the consultancy Gartner Research.
"I recently spoke with a banker who figured out the scam after the initial financial loss for the victim, but before the victim was aware she had been 'taken'," Litan says. "The bank stopped the fraud at the bank's branch when the victim's son came in to make a deposit on her behalf that was going to the scammer."
Customer Education
When it comes to these types of schemes, banks and credit unions need to remember that most of the time, accountholders do not realize they are being taken advantage of by a fraudster, Priess says. When calling accountholders to verify transactions, by asking a few more questions, banking institutions could help customers detect and stop these schemes sooner.
Wesley Wilhelm, a lead fraud expert at NICE Actimize, which provides compliance and anti-money-laundering services to banks and credit unions, says victims are institutions' best hope of thwarting these schemes.
Educating accountholders about the tactics used in these types of attacks could help banks and credit unions raise flags sooner, he says.
"In these cases, the victim frequently has some doubt about the checks," Wilhelm says. "But they go through with the transactions anyway because of the trusted relationship they think they have developed."
Cross-Channel Implications
The use of mobile remote deposit capture, which has facilitated real-time imaged deposits, has breathed new life into sweetheart schemes, says Al Pascual, a senior analyst who researches fraud and security for consultancy Javelin Strategy & Research.
"It seems that thanks to mRDC [mobile remote deposit capture], everything old is new again when it comes to check fraud," he says. "This is no longer a case of a few bad apples re-depositing the same check multiple times. Criminals are actively turning to the sweetheart scam, or compromised or synthetic IDs, to open new accounts, depositing stolen and/or counterfeit checks, and cashing out as soon as the checks clear."
Emerging schemes require banking institutions to have broader views of cross-channel activity and customer behavior, Wilhelm says.
"Banks continue to evolve their deposit account fraud detection solutions," he says. "The best-in-class organizations are deploying enterprisewide, cross-channel systems to evaluate a broader context of activity to detect fraud, and to present the entire context of account activity - deposits and posted checks and changes in behavior - in a single fraud alert."