Business Continuity Management / Disaster Recovery , Fraud Management & Cybercrime , Governance & Risk Management
Ransomware: As GandCrab Retires, Sodinokibi Rises
Ransom Payments to Crypto-Locking Malware Extortionists Are Surging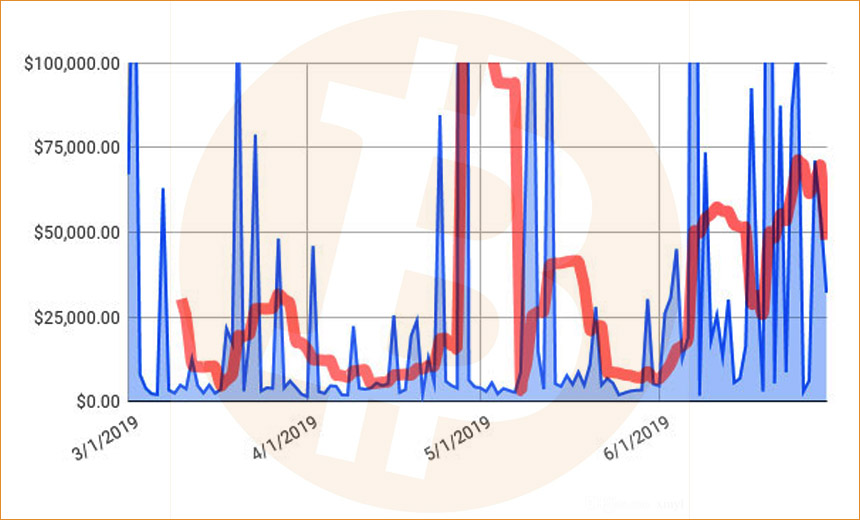
The FBI has published the decryption keys needed to unlock variants of the notorious GandCrab ransomware. Separately, a coalition of American mayors has vowed to never pay ransoms to extortionists. But one security firm reports that victims are collectively paying more in ransoms now than they were at the beginning of the year.
See Also: Cyber Risk Readiness
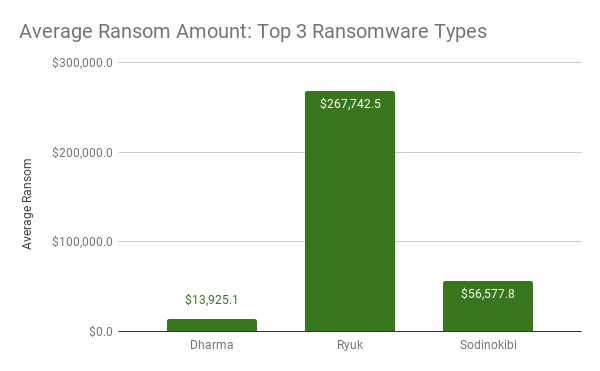
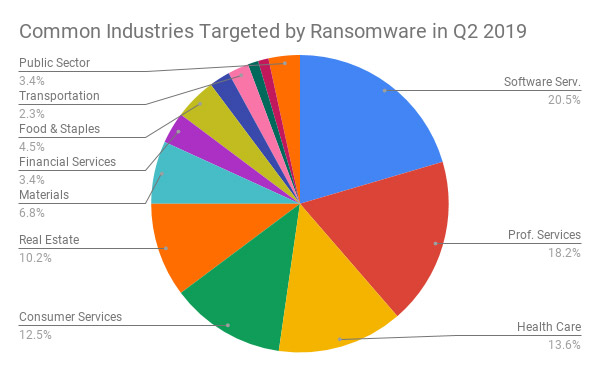
Among all of the many strains of crypto-locking malware being wielded by criminals, however, Ryuk continues to dominate, as do Dharma and Phobos, ransomware incident response firm Coveware says in a new report analyzing ransomware trends for the second quarter of this year.
The gang behind the GandCrab ransomware-as-service offering last month announced its retirement. But a newer RaaS offering called Sodinokibi has quickly moved to seize the suddenly vacant major market share, Coveware reports.
Down and Out in GandCrab Land
GandCrab had been one of the most successful - as in notorious - RaaS offerings since it was first spotted targeting South Korean companies in January 2018. Security experts say "affiliates" could sign up to use GandCrab under terms and conditions that included the GandCrab gang getting a 40 percent cut of all ransoms paid by victims.
The FBI says users of the ransomware quickly began amassing victims in the U.S. after it was first spotted. "GandCrab rapidly rose to become the most prominent affiliate-based ransomware and was estimated to hold 50 percent of the ransomware market share by mid-2018," the FBI says. "Experts estimate GandCrab infected over 500,000 victims worldwide, causing losses in excess of $300 million."
GandCrab Master Key Released
But the tables have recently turned on GandCrab, with the FBI on Monday releasing a flash alert that includes the master keys needed to decrypt GandCrab.
That follows the release on June 17, via the No More Ransom portal, of a free decryption tool for all versions of GandCrab ransomware that have been seen in the wild. The tool was released thanks to the efforts of the FBI, working with eight European law enforcement agencies, as well as Europol - the EU's law enforcement intelligence agency - and Romanian security vendor Bitdefender.
"The collaborative efforts further identified the master decryption keys for all new versions of GandCrab introduced since July 2018," the FBI says, adding that it's released the master keys "to facilitate the development of additional decryption tools."
Previously, law enforcement agencies and security firms had produced free decryptors for some versions of GandCrab. In February, for example, free decryptors could unlock GandCrab versions 1, 4, and 5, up to 5.1. But shortly after those appeared, security experts said the GandCrab team pushed version 5.2, which couldn't be unlocked by the decryptor (see: Police Push Free Decryptor for GandCrab Ransomware).
By June 1, however, two security researchers who have been tracking the GandCrab operation - Damian and David Montenegro - told Bleeping Computer that the GandCrab team had announced its impending retirement.
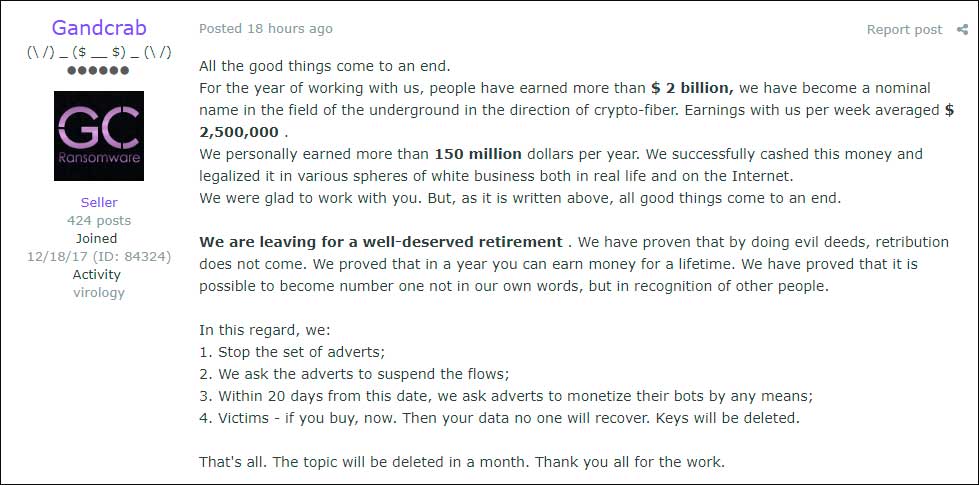
The GandCrab gang's claim that its efforts generated more than $2 billion in illicit profits could not be independently verified.
Despite the sign-off, might GandCrab come back? "If the criminals have shut up shop as they appear to say they’ve done, then hopefully [not]," says Alan Woodward, a computer science professor at the University of Surrey.
.@europol @FBI et al have released the Master Decryption Key for GandCrab https://t.co/XXntRZWscq So now anyone can build a decryptor. There is a tool already at https://t.co/ewHig0RTNT but this hopefully will pull all of its teeth.
— Alan Woodward (@ProfWoodward) July 16, 2019
Criminals Keep Profiting
Despite GandCrab vowing to bow out, ransomware appears to be more lucrative than ever for the criminals that opt to wield it.
"In Q2 of 2019, the average ransom payment increased by 184 percent to $36,295, as compared to $12,762 in Q1 of 2019," Coveware reports. "The increase reflects the growing prevalence of Ryuk and Sodinokibi, variants of ransomware that have rapidly increased their demands. These types of ransomware are predominantly used in targeted attacks on larger enterprises, or on distributed networks of companies via IT managed service providers or hosting ISPs."
Crypto-locking ransomware, which first appeared in late 2013, continues to be big business for criminals. While organizations of all sizes and across every sector, including healthcare, have been targeted, many criminals appear to have recently begun focusing on small municipalities, given their seeming propensity to pay a ransom (see: Second Florida City Pays Up Following Ransomware Attack).
Law enforcement experts have long recommended preparing rather than paying. But the FBI as well as Britain's National Crime Agency say there's no law against paying.
Meanwhile, the count of victims continues to mount. Michael Gillespie (@demonslay335), a U.S.-based developer who runs the free ID Ransomware service to help victims identify what's crypto-locked their system, tells the New York Times that he receives 1,500 requests for help daily.
Gillespie's service recognizes 739 strains or major variants of malware. But as he's told Information Security Media Group, the list isn't meant to be exhaustive.
Economics, if not ethics, drives some victims to pay. When the city of Atlanta got hit by crypto-locking malware in 2018, attackers demanded $51,000 in return for the promise of a decryption key. The city declined to pay, which earned it plaudits.
But that came at a cost: Atlanta Mayor Keisha Lance Bottoms told the U. S. House of Representatives Committee on Homeland Security last month that 15 months after ransomware hit city systems, Atlanta had spent $7.2 million on cleanup costs, which might continue to increase. Some of those costs have been covered by insurance, although city officials haven't said how much (see: Ransomware Increasingly Hits State and Local Governments).
Restoration Is Just the Beginning
Paying is no panacea. Indeed, ransomware victims who pay often find that their challenges are just beginning, security experts warn. First, they're trusting their attacker to furnish them with working decryption software. Even when they do receive it, decryptors for many strains of ransomware are built to restore files, but not file hierarchies, which require time-consuming, manual efforts to rebuild. And not all decryptors are 100 percent effective at restoring files, meaning some files still get lost.
In the second quarter of this year, Coveware reports that "victims who paid for a decryptor recovered 92 percent of their encrypted data," although the success varied dramatically based on the strain of crypto-locking code that hit them.
"For example, Ryuk ransomware has a relatively low data recovery rate, at around 87 percent, while Sodinokibi was close to 100 percent," Coveware says. "Data loss is typically a result of a flawed encryption process where files are partially encrypted or wiped. Some clients reduce the expense of running inefficient decryptor tools and simply archive non-essential encrypted data for a rainy day."
Even when decryptors work, they can also be slow. In June, for example, the city of Lake City, Florida, got hit by a ransomware attack that crypto-locked about 16 terabytes of data, with attackers demanding a ransom. Joseph Helfenberger, the city manager, tells the New York Times that the city's insurer - the Florida League of Cities - negotiated a settlement of 42 bitcoins, then worth about $460,000, with the attackers, with the city paying a $10,000 deductible. Once it paid the ransom, the city received a working decryptor.
But restoration efforts have been slow, with Helfenberger saying that each terabyte has taken about 12 hours to recover.
Recommendation: Invest in IT
Security experts say Lake City's ransomware outbreak is yet another reminder that preparing for a ransomware attack costs much less than sustaining one. Lake City, for example, is reportedly now implementing a cloud-based backup system that will cost $60,000 per year.
"Good IT operations, which include robust backup systems and business continuity planning, are essential in the defense against many threats, including ransomware," says Brian Honan, president of Dublin-based cybersecurity consultancy BH Consulting, in a recent SANS Institute newsletter.
"The sum of $460,000, plus the cost of downtime incurred and other professional services engaged in the recovery, would no doubt have been a better investment in better IT rather than funding criminal activity," he says. "We should use these examples to educate senior management as to why paying for robust IT is not a cost but rather an investment."
US Mayors Vow to Not Pay Ransoms
Calls to stop paying ransoms continue to grow. Last month, the U.S. Conference of Mayors passed a resolution that opposes paying ransomware attackers. The organization notes that "at least 170 county, city or state government systems have experienced a ransomware attack since 2013," with 22 of those attacks having occurred this year.
"Now, therefore, be it resolved, that the United States Conference of Mayors stands united against paying ransoms in the event of an IT security breach," the resolution reads.
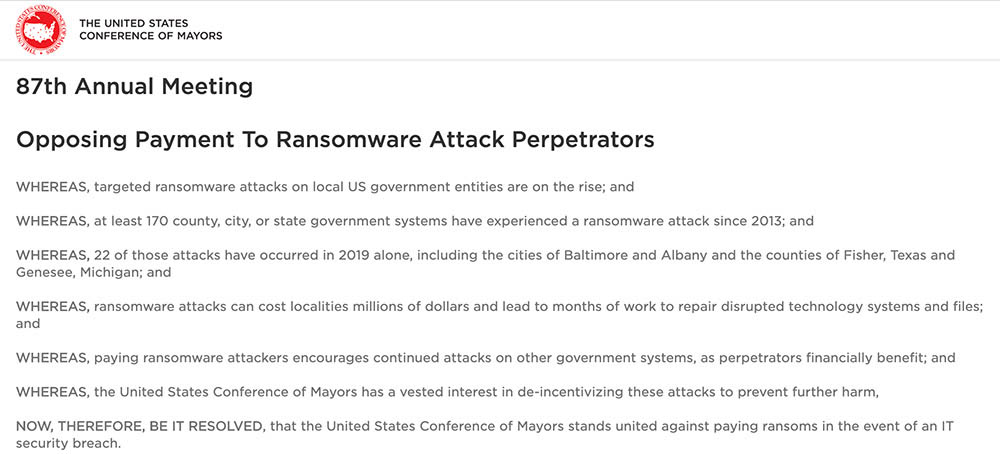
“Paying ransoms only gives incentive for more people to engage in this type of illegal behavior," Baltimore Mayor Jack Young told CBS Baltimore (see: Baltimore Ransomware Attack Triggers Blame Game).