Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management
'Sea Turtle' DNS Hijacking Group Conducts Espionage: Report
Cisco Talos Researchers Describe Group's Methods
A nation-state sponsored espionage campaign dubbed Sea Turtle has been manipulating the domain name system to target more than 40 organizations, including intelligence agencies - especially in North Africa and the Middle East, Cisco Talos warns. Experts say defenses against DNS hijacking lag.
See Also: The State of Organizations' Security Posture as of Q1 2018
The attacks are designed to spoof websites to steal credentials and passwords in an effort to gain greater access to the networks of these organizations, according to the Cisco Talos analysis. The ultimate goal is to spy on these networks to gain intelligence.
This complex operation takes advantage of some of the weaknesses in the old DNS protocols. The attackers use a variety of techniques to avoid detection, including faking security certificates and credentials, the researchers say.
The Sea Turtle attacks, which started as far back as January 2017, are continuing, the Cisco Talos researchers say. Although the researchers claim to know the nation-state behind these attacks, they don't name the country.
Cisco Talos does not believe the Sea Turtle campaign is related to another DNS hijacking campaign called DNSpionage, which the U.S. Department of Homeland Security warned about earlier this year. Several security vendors, including FireEye, have blamed that attack on Iran.
These types of attacks that target DNS have increased, with security researchers warning that the DNS protocols, some of which were designed without security in mind, need to be rethought. At this year's RSA conference, some security experts called for the more rapid implementation of Domain Name System Security Extensions - DNSSEC - which can help better secure DNS.
"The transition to DNSSEC has taken 20 years, but it's plodding along and making a difference," independent security expert Paul Kocher told the RSA audience in March.
The problem is that the threat actors targeting DNS flaws are also changing their tactics, Craig Williams, a director at Cisco Talos, tells Information Security Media Group.
"These actors taking advantage of the way the DNS system works," Williams says. "People are trying to add security to DNS, but it's a tricky problem, with the bad guys constantly trying to find new ways to evade and manipulate the system."
Understanding Sea Turtle
The Sea Turtle attacks start by targeting the weaknesses in DNS - which acts as a "phone book" for the internet. DNS takes the domain names we use every day and translates them into a numeric code that helps the computer find what the user is looking for.
While the hijacking of DNS is central to this type of attack, it's the not the ultimate goal, according to Talos researchers. Instead, the threat actors' goal is to steal user and administrative credentials to gain access to networks and other systems of interest and then conduct spying operations.
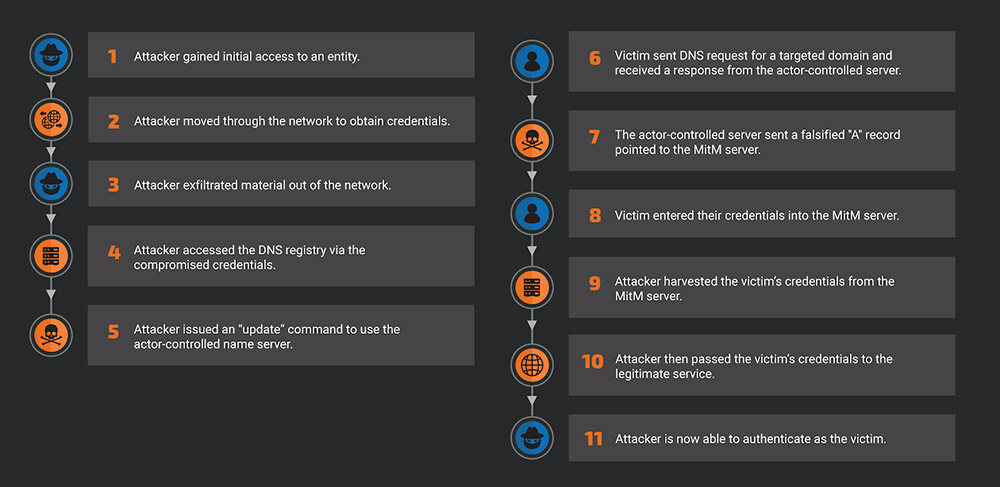
To achieve that goal, the Sea Turtle group establishes a way to control the DNS traffic of the target. It modifies DNS records to point users to malicious servers that the threat group controls and then captures the credentials so it can hack deeper into various systems.
The Sea Turtle group's main targets are ministries of foreign affairs, military organizations, intelligence agencies and prominent energy companies, the researchers say. Because of the complexity of the operation, there are a host of secondary victims, including telecommunications organizations, ISPs, IT firms and DNS registrars, Cisco Talos notes.
Manipulating Traffic and Victims
The Sea Turtle group starts these campaigns by taking advantage of several types of known vulnerabilities, according to Cisco Talos. These include:
- CVE-2009-1151: A PHP code injection vulnerability affecting phpMyAdmin;
- CVE-2017-3881: A remote control exploit, or RCE, by an unauthenticated user with elevated privileges for Cisco switches;
- CVE-2017-6736: An RCE for Cisco integrated service router 2811;
- CVE-2017-12617: An RCE affecting Apache web servers running Tomcat
On at least one occasion, the Cisco Talos team found that the Sea Turtle group used spear phishing as part of the initial attack.
Next, the threat actors modified the nameserver or NS records of the organization, allowing them to manipulate the DNS register and point traffic toward a server that they controlled. This malicious server then allowed the threat group to control any and all DNS inquiries from the target's machine, the researchers found.
From there, the attackers created a man-in-the-middle framework that looks like a legitimate service, but its true purpose was to capture credentials and passwords. To give it an air of legitimacy, the group performed a "certificate impersonation," essentially using a security certificate from another provider for the same domain, which made detecting the attack difficult because the website still displays the SSL "padlock," according to Cisco Talos.
Once those credentials and passwords were captured, the initial victim was then sent back to a legitimate DNS protocol, and the Sea Turtle group could then start further penetrating the target network. For instance, they stole the primary target's SSL certificate almost immediately to create more man-in-the-middle attacks and continue to steal credentials and burrow further into the network, the researchers found.
"The stolen certificates were typically only used for less than one day, likely as an operational security measure," the researchers write. "Using stolen certificates for an extended period would increase the likelihood of detection. In some cases, the victims were redirected to these actor-controlled servers displaying the stolen certificate."
The Sea Turtle group is also proficient at impersonating legitimate VPN applications, such as the Cisco Adaptive Security Appliance, to perfect the man-in-the-middle attacks, Cisco Talos reports.
The group also attacked specific DNS registrars, some of which control top-level domains - including many .com addresses - in order to change the DNS details and trick the victims into thinking they were landing on a legitimate website.
At one point, Cisco Talos researchers found that the Sea Turtle group hijacked the traffic of Sweden's Netnod, a DNS provider.
In February, Netnod released a statement acknowledging it had been a victim of a man-in-the-middle attack. In this case, the attackers were able to gain the credentials of the administrators of the top-level domain of Saudi Arabia (.sa), according to the researchers.
Likely to Continue
The Sea Turtle group is continuing to target primary and secondary victims in at least 13 countries, Cisco Talos reports. Williams tells ISMG that the researchers have reached out to the organizations that have been targeted.
"It's unlikely this activity will go away soon," Williams says. "Generally, we see people copycat this behavior for other purposes."
To help mitigate the risk of this kind of DNS attack, Cisco Talos recommends organizations use a registry lock service that will require an out-of-band message before any changes are made to the DNS record.
Organizations can also require the use of multifactor authentication to access DNS records and check to see if they have been manipulated. Cisco Talos also recommends conducting a networkwide password reset and applying all patches to internet-facing machines.