Sponsored by CrowdStrike
Sponsored by Palo Alto Networks
Comprehensive and Proactive Security Operations for Financial Services
Sponsored by Splunk
Top 50 Security Threats
Sponsored by Splunk
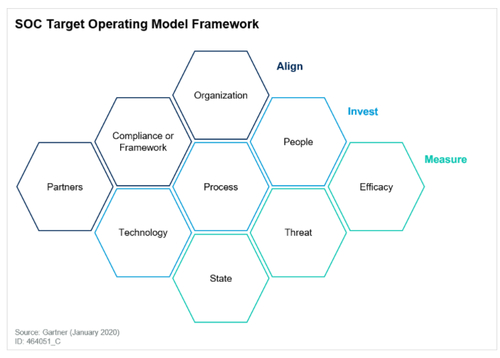
Gartner® Report: Create an SOC Target Operating Model to Drive Success
Sponsored by Graylog
What to Consider When Selecting a Source of Threat Intelligence
Sponsored by Splunk
Securing Complexity: DevSecOps in the Age of Containers
Sponsored by ServiceNow
ESG SOAR and MITRE ATT&CK
Sponsored by Splunk
The SOAR Buyer's Guide
Sponsored by Splunk
The 10 Essential Capabilities of a Best-of-Breed SOAR
Sponsored by Graylog
Leveraging a Highly Effective Combination of Human and Machine Power
Sponsored by Sysdig
Securing Kubernetes Checklist
Sponsored by Splunk
How to Uplevel Your Defenses with Security Analytics
Sponsored by Splunk
The Fundamental Guide to Building a Better Security Operation Center (SOC)
Sponsored by Rapid7
Choosing the Right Detection and Response Solution for your Business
Sponsored by Palo Alto Networks