Sponsored by Juniper Networks
Sponsored by Sophos
The Evolution of Automated, Active Attacks
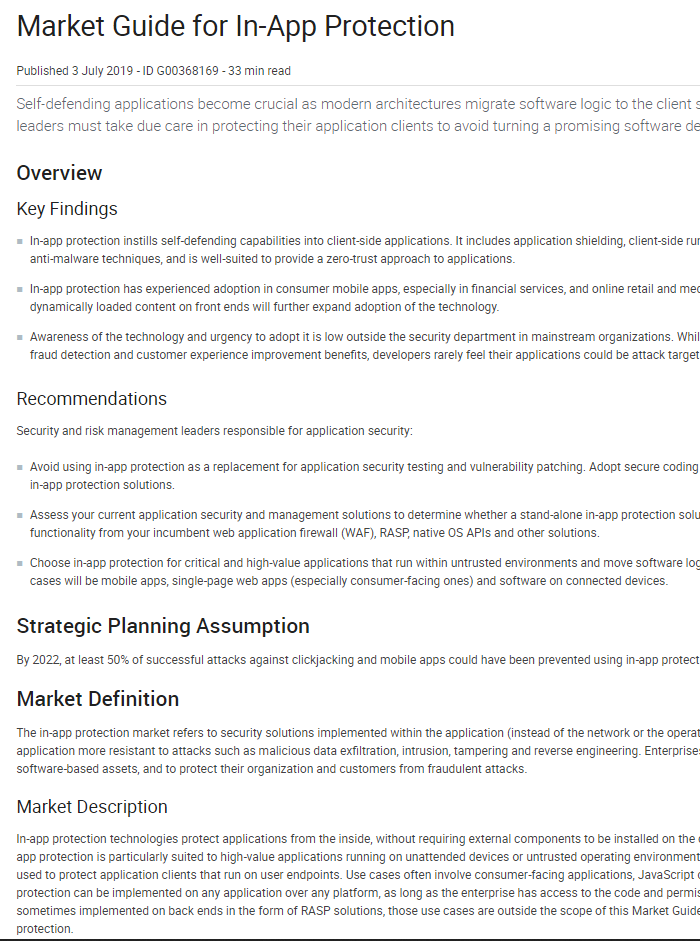
Sponsored by Arxan
Gartner Market Guide for Application Shielding
Sponsored by SecPod
Cyber Hygiene Automation: Prevent Exposure to Cyber Attacks
Sponsored by SecPod
Cyber Security Resilience and Defense-in-Depth: A New Dimension
Sponsored by Core Security, a Helpsystems Company
How to Identify Compromised Devices with Certainty
Sponsored by Cymulate
Are You APT-Ready? The Role of Breach and Attack Simulation
Sponsored by Symantec
Adapting to the New Reality of Evolving Cloud Threats of 2019
Sponsored by Symantec
2019 Internet Security Threat Report
Sponsored by Aqua Security
Securing Container and Cloud Native Applications - An Illustrated Guide
Sponsored by Aqua Security
eBook: Container Security: 10 Things DevOps Need To Do
Sponsored by Malwarebytes
Malware: The Evolution of Exploits & Defenses
Sponsored by Zscaler
State of Digital Transformation Report - EMEA 2019
Sponsored by nCipher
Bring Your Own Key (BYOK): When Cloud Convenience Meets Security
Sponsored by GuardiCore