Sponsored by JFrog
Sponsored by JFrog
Security and Compliance of the Open Source Software Dependencies You Rely On
Sponsored by 1Password
Securing Your Business Begins with Password Security
Sponsored by VMware
VMware Carbon Black App Control
Sponsored by Zscaler
Evolving Alongside CMMC 2.0: Helping Organizations Meet CMMC Compliance
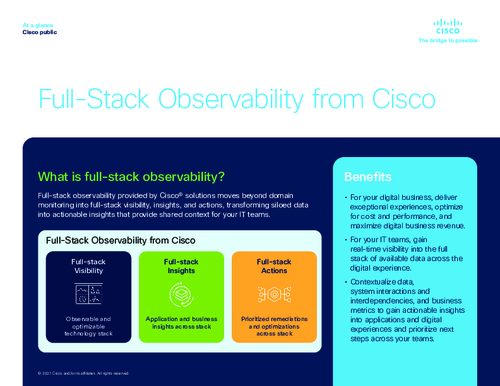
Sponsored by Cisco
Guide: How to Get Full Visibility Across Your Infrastructure
Sponsored by Palo Alto Networks
Zero Trust Enterprise for Healthcare Organizations
Sponsored by Dell Inc.
eBook I The Periodic Table of Data Protection
Sponsored by Hexagon
Seven Experts on Balancing Digital Transformation and OT Security
Sponsored by Secure Code Warrior
The State of Developer-driven Security, 2022
Sponsored by Cyberark
CyberArk Privileged Access Management Solutions
Sponsored by Onspring
5 Reasons Why Automation is the Next Step for Your Business
Sponsored by Proofpoint