Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response
Winter Olympics Gold Medal for False Flag Goes to ... ?
Researchers: To Foil Attribution, Attackers Planted Code Previously Tied to Lazarus Group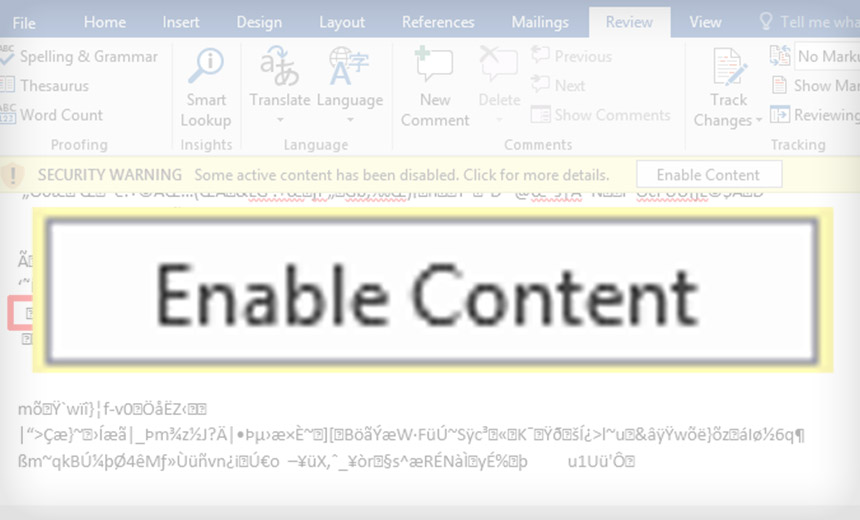
Whoever unleashed malware built to disrupt last month's Winter Olympics in Pyeongchang, South Korea, designed it to look like it had been executed by a group of hackers tied to North Korea.
See Also: 10 Incredible Ways You Can Be Hacked Through Email & How To Stop The Bad Guys
Security researchers at Moscow-based security firm Kaspersky Lab say that numerous clues point to attackers having run "an intricate false flag operation" by planting code previously seen in attacks tied to a hacking group called Lazarus.
The U.S. government, among others, says that Lazarus - also known as APT37, Group 123, Hidden Cobra and Reaper - is tied to the Pyongyang-based government of North Korea. The group has also been fingered as being behind numerous high-profile attacks against banks and cryptocurrency exchanges, including the 2016 heist of $81 million from the central bank of Bangladesh's account at the Federal Reserve Bank of New York, perpetrated via fraudulent SWIFT interbank money-moving messages (see Bankshot Trojan Targets Turkish Financial Sector).
The malware used against the Olympic Winter Games, named "Olympic Destroyer" by researchers, wreaked havoc just before the opening ceremonies, including disrupting attendees' ability to print tickets or use WiFi. At the time, the International Olympic Committee confirmed to Information Security Media Group that the disruptions "were caused by a cyberattack." But the IOC refused to speculate about who might have launched the attack (see Attribution Games: Don't Rush to Blame).
Further complicating any attempt to attribute the attack: Vitaly Kamluk, head of the APAC research team at Kaspersky Lab, said at the firm's Security Analysts Summit last week that he believes that Olympic Destroyer was designed to be a false flag operation.
"We can say with 100 percent confidence that the attribution to Lazarus is false," he told summit attendees, the Register reports.
Costin Raiu, director of Kaspersky Lab's global research and analysis team, says the "subtle false flag" may well have been designed to sow doubt and confusion over the attackers' identity and future efforts to attribute any malware attacks to a specific group or nation-state.
Among the false flags, Olympic Destroyer includes a rich header - an undocumented structure created whenever code gets generated in Microsoft Visual Studio - that is identical to Bluenoroff malware previously tied to Lazarus. Many malware researchers look at rich headers to help determine whether or not code matches previously seen samples.
But Kaspersky Lab has concluded that the rich header in many versions of Olympic Destroyer malware was forged, having been "deliberately copied from the Bluenoroff samples," in part because it has no connection to the contents of the binary file in which it appears.
"It is not possible to completely understand the motives of this action, but we know for sure that the creators of Olympic Destroyer intentionally modified their product to resemble the Bluenoroff samples produced by the Lazarus group," Kaspersky Lab says.
The #OlympicDestroyer wiper's Rich header is forged to make it look like the Lazarus group. This is a subtle false flag the attackers hoped that the industry will find. #TheSAS2018 pic.twitter.com/H5t94rVtea
— Costin Raiu (@craiu) March 8, 2018
The security firm adds that while Olympic Destroyer was designed to wait for 60 minutes before shutting an infected PC down and leaving it unbootable, its researchers have now found a subsequent version in which the time delay was removed. This version appears to have been unleashed after the main attack began, suggesting that "the attackers were probably in a rush and didn't want to wait before shutting down the systems" at additional targets.
In the later version of the malware, however, the attackers failed to fake the rich header information by cutting and pasting the version from Bluenoruff, the Kaspersky Lab researchers say.
Spear-Phishing Emails
Previous researchers have detailed how the Olympic Destroyer malware functioned (see Hackers Win Olympic Gold Medal for Disruption).
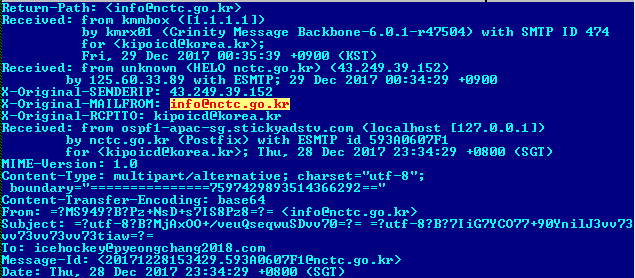
In its latest research, meanwhile, Kaspersky Lab reports that the malware appears to have been carried by spear-phishing emails with a Winter Olympics theme that in some cases were addressed to "icehockey@pyeongchang2018.com" - and cc'd to victims. The emails, which first began appearing last December, carried malicious Microsoft Office attachments.
"The documents contained nothing but slightly formatted gibberish to make it look like the text had an encoding problem, encouraging the user to press a button to 'enable content,'" Kaspersky Lab says.
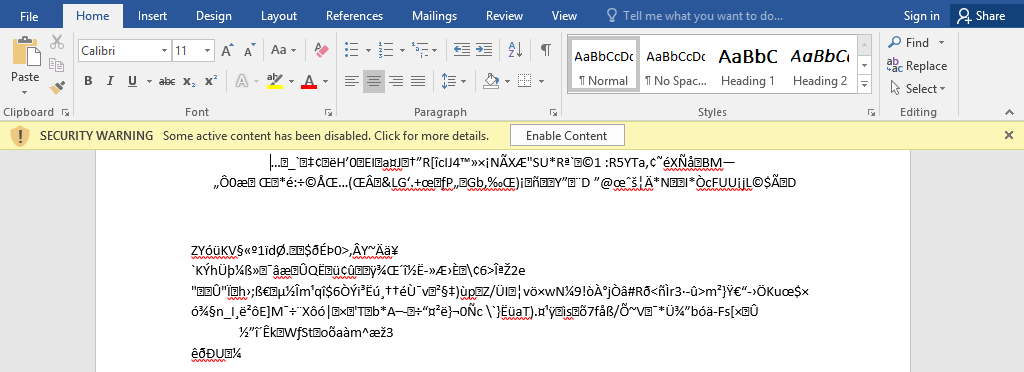
"When the victim 'enables content,' the document starts a cmd.exe with a command line to execute a PowerShell scriptlet that, in turn, downloads and executes a second stage PowerShell scriptlet and, eventually, backdoors the system," after which wiper malware gets unleashed, it adds.
"The only apparent links between this email campaign and Olympic Destroyer would have been the target; however, we managed to discover a couple of connections between this weaponized document and the attack in Pyeongchang which makes us believe they are related," Kaspersky Lab says, citing partially redacted IP addresses, email addresses and virtual server registrant details.
The security firm says it's shared that information with law enforcement agencies.
Olympic Destroyer Includes Reused Code
An analysis of the Olympic Destroyer malware was first published by information security researchers at Cisco's Talos group, who also studiously avoided attributing the attack to any group of nation. Other security researchers noted that code in the malware had been seen in previous attacks tied to multiple groups, including those with apparent ties to not just North Korea but also China and Russia.
Malicious code reuse does not a smoking gun make. Anyone can cut and paste attack code. Knowing who was sitting behind the keyboard, however, is an entirely different matter and often requires "sources and methods" - government-speak for not just technical but also highly sensitive human intelligence of the type gathered by spy agencies (see Beyond a Reasonable Doubt? Assessing Kremlin's Role in Hack).
Motive: Plausible Deniability
Security firms continue to caution that just because code appears in malware, that doesn't mean that an attack has been launched by the same group.
On Feb. 26, Cisco Talos published a blog post titled, "Who Wasn't Responsible for Olympic Destroyer?"
"The threat actor responsible for the attack has purposefully included evidence to frustrate analysts and lead researchers to false attribution flags," write Cisco Talos researchers Paul Rascagneres and Martin Lee.
That subterfuge could be designed to give the actual attacker plausible deniability if different security firms rushed to attribute based on code samples. "This false attribution could embolden an adversary to deny an accusation, publicly citing evidence based upon false claims by unwitting third parties," the researchers write. "This must force one to question purely software-based attribution going forward."
Attribution Follies
The difficulty - and geopolitical dangerousness - of attributing malware to any specific group or nation-state has led many security experts to argue that attribution is best left to governments. Furthermore, experts say, in the wake of any hack attack, breached businesses are better off devoting resources to identifying what happened and preventing a recurrence (see Breach Attribution and 'Hack Back': Don't Waste Time).
For governments, publicly attributing an attack is a diplomatic matter (see Trump Administration: 'North Korea Launched WannaCry').
In rare cases, attribution has been included in U.S. criminal indictments filed against individuals who allegedly participated in nation-state attacks, including Chinese nationals for hacks of the health insurance company Anthem and the U.S. Office of Personnel Management, as well as 13 Russian individuals and three organizations charged with running a social media manipulation campaign designed to interfere in the U.S. political process (see Anatomy of a Russian Information Warfare Campaign).
It's unlikely that the indicted individuals will ever seen the inside of a U.S. court room, provided they don't attempt to vacation in or travel via countries that have extradition treaties with the U.S. But such indictments do appear to be a U.S. government attempt to at least hold foreign governments and their alleged agents publicly accountable for hack attacks (see Putin Offers Extradition Promise to US: 'Never').